You keep seeing constant UFO news and UAP disclosure claims, and the signal-to-noise ratio is brutal: recycled lore gets reposted as “new,” while the few things that would actually matter are buried in vague screenshots and secondhand summaries. One of those potentially consequential claims is that Ecuador’s Defense Ministry is reported to have created a formal UAP and UFO investigation capability in 2005, often referred to as “CEIFO,” which, if substantiated, would predate today’s disclosure wave by years.
The decision you’re trying to make is simple: treat this as credible government provenance, or file it under internet folklore. You’re not looking for social-media certainty; you’re looking for documentation that reads like a real ministry function, with a mandate, an owning office, and a traceable paper trail. That’s the tension this story creates: the 2005 claim is compelling precisely because it would establish an early precedent, but the verification trail in the provided materials is thin, so this post separates what can be supported from what gets inferred.
Here is the constraint up front: none of the provided source documents contain any mention of CEIFO by name, and none of them link “CEIFO” to Ecuador, a defense ministry, or UAPs. Complicating it further, “CEIFO” in the provided sources expands as “Centre for Research in International Migration and Ethnic Relations,” a Stockholm University-affiliated research center, not an Ecuadorian defense unit. The provided sources also do not provide a Spanish-language expansion or rendering of the acronym CEIFO, which removes a key cross-check you would normally use to validate an alleged government entity.
What remains, then, is a disciplined way to judge the claim: what conditions in 2005 would make a defense-run reporting channel plausible, and what specific paperwork would have to exist for the story to move from assertion to record.
You’ll walk away with an evidence-first framework to understand the 2005 claim, what a real defense UAP unit would look like on paper, and how to evaluate new disclosure narratives without outsourcing your judgment to hype.
Why 2005 was a turning point
In 2005, formal handling of unidentified aerial reports aligned with core defense and aviation realities in Ecuador and across the region. Airspace awareness had become a day-to-day operational requirement: if a radar scope shows an unknown track, or a crew files a safety report about an uncorrelated contact, somebody in government has to decide whether it is an airliner, a misidentified known aircraft, a smuggling flight, or an actual violation of restricted airspace. Treating those inputs as “unusual” without a formal channel wastes time, fragments responsibility, and increases the odds that the next report arrives too late to act.
The same airspace-security logic shows up in how institutions talk about risk. Ecuadorian policy emphasis on dismantling clandestine airstrips and restricting UAV operations near detention centers is not a curiosity, it is a signal: the state was actively treating uncontrolled aviation activity as a security problem that demanded rules, enforcement, and reporting. Under that posture, “UAP-style” reports are an expected byproduct of tighter airspace control, not evidence by themselves of anything exotic.
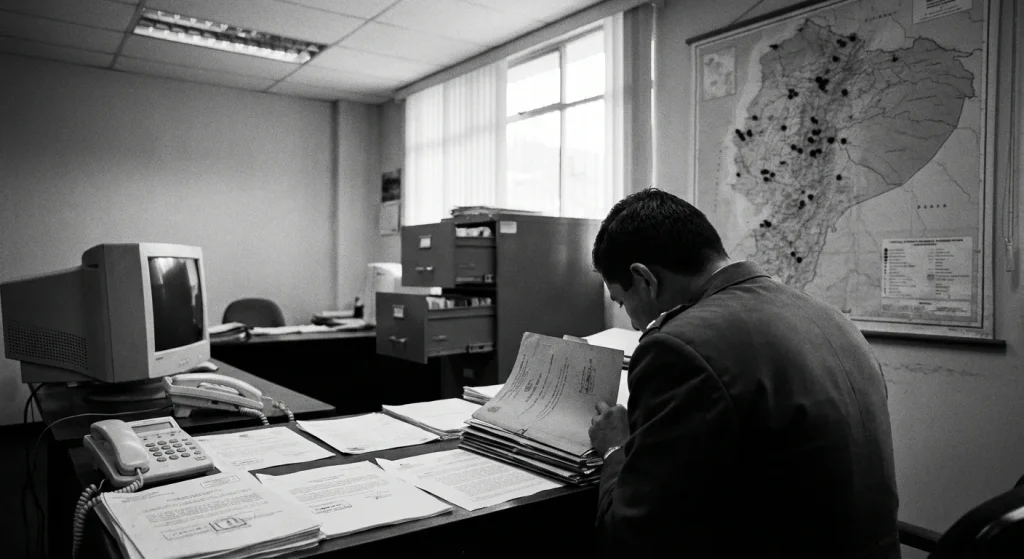
Ecuador’s defense governance structure makes it straightforward to see where an investigative capability could be sponsored. The Ministry of Defence functions as the political, strategic, and administrative organ of national defence, the place that sets direction and legitimizes programs. The Joint Command of the Armed Forces is the highest organ of the armed forces, the place that coordinates across services and turns national defense priorities into operational tasks.
That division of labor matters because it explains why a formal pathway for unusual aerial reporting is institutionally rational. Strategic leadership can authorize a standardized intake and accountability mechanism, while the operational side can route reports through existing air-defense, aviation-safety, and intelligence functions. None of this requires assuming a sensational mission; it matches how defense systems normally manage ambiguous information that affects flight safety and sovereignty.
Detection capacity drives reporting volume. The United States donated a modernized TPS-43 surveillance radar to Ecuador to strengthen airspace control and aircraft detection.
More surveillance means more tracks to reconcile, more opportunities for sensor glitches, more cases where an aircraft is seen by one system but not another, and more pressure on pilots and controllers to file “something happened” reports when correlation is missing. The friction is predictable: better detection does not only improve coverage, it increases the number of anomalies that must be triaged, documented, and explained in a defensible way.
If you want a practical way to evaluate claims about any alleged “UAP unit,” start with motive. Look first for signs of an airspace safety and security mechanism: links to air-defense or aviation authorities, emphasis on incident documentation, and alignment with sovereignty enforcement priorities. Then ask what proof exists of a distinct unit, because the operational drivers alone explain why governments build the reporting pathway in the first place.
That distinction-between plausible operational need and proven institutional existence-is exactly where the CEIFO claim lives, and it sets up the central question: what, if anything, can be said about CEIFO from the sources actually on the table?
Inside CEIFO and its mission
A defense-run investigative lane is the real story, not the mythology. If an entity like CEIFO existed in the form often claimed, its institutional significance would be simple and concrete: it would move UAP and UFO reporting out of rumor loops and into a defense-managed process where intake, classification, and recordkeeping are mandatory, not optional.
What we can confirm from the provided sources is mostly negative: they do not substantiate an Ecuadorian CEIFO mandate, staffing model, named leadership, participating agencies, or documented procedures. Several excerpts are unrelated to any such unit, and at least one explicitly reflects that “CEIFO” is not mentioned in the material supplied, which means readers should treat any Ecuador-specific structure claims as unverified unless backed by primary documents.
What follows, therefore, is inferred and modelled: a generic scaffold based on how defense and aviation organizations typically run incident investigations when they intend the output to be actionable, auditable, and retrievable. It is not a CEIFO description, and it should not be read as one.
In the provided sources, “CEIFO” is used in the context of an academic research center associated with migration and ethnic-relations work, so any Ecuador usage needs primary-document confirmation rather than acronym matching.
Terminology is not cosmetic inside official reporting systems because the label determines whether a report is treated as an operational anomaly, a flight safety issue, an intelligence concern, or a cultural distraction. Modern bureaucracies increasingly prefer UAP (Unidentified Anomalous Phenomena) because it frames the problem as an unresolved observation that can include multiple domains and sensor modalities, which reduces the stigma that keeps military and civilian professionals from filing clean, timely reports.
The legacy public term UFO (Unidentified Flying Object) describes an object seen in the sky, but it also carries decades of pop-culture baggage that pollutes the evidentiary chain before the first radar log is preserved. In practice, the word choice shapes behavior: pilots and controllers are more likely to document “anomalous phenomena” as an operational deviation worth logging, while “UFO” often invites narrative, interpretation, and premature conclusions that investigators then have to subtract from the record.
A credible investigative unit lives or dies on workflow discipline. The hard part is not “finding aliens,” it is standardizing messy incident data across units, sensors, and human observers while preventing rumor from contaminating the case file. Defense and aviation organizations codify this kind of repeatable process in doctrine and standards documents. AFTTP 3-4.7, for example, is explicitly a tactics, techniques, and procedures publication for contingency response forces, and the NWCG Standards for Helicopter Operations establishes the standards by which helicopter operations are to be conducted. Those are different missions, but the management principle is the same: written procedures turn chaos into comparable records.
- Intake: Accept reports from the people and systems that actually see anomalies in operational contexts, including military pilots, civilian flight crews, radar operators, air traffic control (ATC), and ground observers. The practical objective is fast capture of who observed what, on what channel, and under what duty status, so the report is traceable and not just “something someone heard.”
- Triage: Sort reports by safety and security urgency first, then by misidentification risk. A near mid-air, an airspace incursion, or interference with navigation and comms gets immediate escalation. A single-witness visual report with no supporting sensor data gets a different handling path because the probability of conventional explanation is higher and the investigative cost needs to match the risk.
- Data capture: Lock down the basics that make reconstruction possible, including time, location, altitude, heading, speed estimates, weather, and relevant NOTAM context, plus sensor logs (radar tracks, EO/IR metadata where available), ATC recordings, and witness statements taken while memories are fresh. The goal is to preserve raw artifacts before retellings “improve” the story.
- Classification: Separate “unknown” from “sensitive.” “Unknown” is an evidentiary state: the unit cannot identify the observation with available data. “Sensitive” is a handling constraint: the case file may include capabilities, flight profiles, sensor parameters, or operational details that require restricted distribution even if the object is ultimately mundane.
- Resolution and closure: Close cases as identified (balloon, aircraft, atmospheric effect, sensor artifact, training activity) or unresolved. Closure also includes lessons learned, such as changes to reporting forms, sensor synchronization, or ATC coordination that reduce repeat ambiguity. An unresolved outcome is still useful if the record is complete and comparable.
- Archival: Apply records retention rules so cases are retrievable by date, airspace, unit, sensor type, and disposition. If reports cannot be found later, the unit cannot do trend analysis, cannot answer oversight queries, and cannot prove it handled incidents consistently.
Credibility is procedural, not cinematic. A serious unit defines escalation criteria, document controls, and accountability so that every handoff is auditable. Operational frameworks routinely assign explicit responsibility to named roles; for example, the Task Force Leader is responsible for managing all aspects of a mission, including operational functions. An investigative shop needs the same clarity so “who owned the decision” is never ambiguous.
Reporting lines are the next credibility test, but they have to be described carefully. In a typical model, an investigative cell reports either to ministry-level oversight (for policy, resourcing, and lawful handling of sensitive information) or through joint command coordination (for rapid tasking across air, maritime, intelligence, and civil aviation stakeholders). Both patterns exist in real-world incident management; neither should be asserted as Ecuador-specific without primary documentation.
The real friction point is data integrity: inconsistent timestamps, unsynchronized sensors, missing comms recordings, and post-event storytelling can destroy case value faster than any lack of conclusions. A unit that cannot standardize intake and preserve raw artifacts will generate heat, not insight.
The actionable takeaway is straightforward: treat mandate plus documented workflow as the credibility test. Dramatic claims are cheap. A credible unit proves itself with published authority, repeatable procedures, and records that can be retrieved, reviewed, and compared across cases.
That procedural standard is also the cleanest way to think about what CEIFO supposedly produced: not beliefs or narratives, but logs, case files, and preserved artifacts that an outsider could trace.
What CEIFO investigated and recorded
Claims live or die on documentation. A “government UFO cover-up” becomes testable only when you can point to records: what was logged, what was preserved, and what an outside party can independently check. Without that paper trail, you are left with stories that cannot be falsified.
The quantitative gap is stark: none of the provided source documents contain any statement or data attributable to CEIFO about numbers of reports received, numbers investigated, categories of explanations, or percent unresolved. The supplied sources are largely about unrelated topics (accounting research, systematic review methods, socio-economic studies, OECD and EU policy reporting, education dissertations, and migration research), so they do not function as CEIFO’s statistical ledger.
A credible investigative unit is defined less by what it “believes” and more by what it can document consistently. In practice, the intake stream for an official UAP office typically clusters into a small set of report types that generate specific record artifacts.
Expect reports such as pilot observations (narratives tied to flight data), radar tracks (raw plots and processed outputs), air traffic control anomalies (logs, audio, incident notes), civilian reports routed through authorities (statements, call logs, referral memos), and photos or video that retain original metadata (device data, timestamps, file hashes). The record artifacts matter because they determine whether a claim can be reconstructed later or dies as hearsay.
The non-obvious complication is that most incidents arrive under-documented. When a file stays “unresolved,” that status usually reflects insufficient data, not an extraordinary conclusion. That is why serious programs also standardize resolution categories: misidentifications (aircraft, balloons, astronomical objects), sensor artifacts (processing errors, calibration issues, multipath), and weather effects (cloud layers, lightning, temperature inversions), plus a smaller remainder that cannot be closed because the evidentiary floor was never met.
Evidence quality is mostly process. “Chain of custody” is the documented control history of a file or physical item, and it is what keeps a photo, video, or sensor export rumor-resistant by proving who handled it, when, and how it was stored. “Multi-sensor corroboration” is agreement across independent sources (for example, visual observation plus radar plus ATC audio), and it is the fastest way to separate perception errors from an external event because each sensor has different failure modes.
- Identify the observer and training level (pilot, ATC, maintenance, civilian) and capture contact details for follow-up.
- Pinpoint exact time and location (timezone, coordinates if possible), plus altitude and heading if airborne.
- Measure duration and changes over time (start, end, maneuvers, intermittency).
- Log environmental conditions (visibility, cloud cover, wind, precipitation, celestial objects visible).
- Preserve sensor data availability (radar, ADS-B, ATC audio, onboard systems) and request raw exports, not screenshots.
- Retain original files with intact metadata; avoid re-encoding, filters, messaging apps, and social uploads as the “master.”
- Separate witnesses before detailed discussion to reduce memory convergence; record independent statements.
- Document custody steps: who copied what, where it was stored, hashes if created, and any transfers.
This is a search blueprint, not proof about Ecuador. Public signals usually surface where governments store or release primary documents: archives, declassification portals, and agency series that can be queried by date, office, and subject.
As a model of what a mature declassified-document repository looks like, the Digital National Security Archive (DNSA) is described as the most comprehensive set of declassified government documents available. That “repository first” structure is the pattern to look for, even when the country and portal differ.
Canada Declassified is a useful analogy for publication mechanics: it is a digital repository of government records declassified under the Canadian Access to Information Act. The key lesson is procedural, not geographic: declassification can be routinized into searchable releases rather than ad hoc leaks.
The Office of the Information Commissioner publication provided outlines proposals for a possible declassification strategy for national security and intelligence records, showing that declassification can be systematized as a program with defined workflows.
Practical hunting starts with finding the right catalogs and series. Library and archival guides that point to major government-document collections and declassification projects are often the shortest path to registry entries, finding aids, and record group descriptions that reference the documents you actually need.
The actionable takeaway is simple: prioritize primary documents (founding instruments, ministry memos, registry entries, archival references) over recycled anecdotes. Use the checklist above as your filter for any CEIFO-related claim or the next viral “new UAP” story.
That evidence discipline also clarifies why comparisons to the modern UAP moment can help: today’s public conversation has forced some governments to build visible structures, which makes “what real looks like” easier to benchmark.
CEIFO compared to today’s UAP push
The global UAP disclosure conversation did not invent the idea of institutionalizing anomaly reporting. It formalized it into repeatable governance: named offices, mandated reporting, and oversight that creates public pressure. That pattern is exactly why a purported 2005 Ecuador move is strategically interesting in hindsight, because it treats anomalies as an administrative category the state must capture and route, not a rumor the state can ignore.
Modern disclosure is not primarily a story about dramatic revelations. It is a story about bureaucratic durability. Once a government creates an office with a defined remit and ties it to recurring legal authorities, “disclosure” becomes something that can be audited: guidance gets published, reporting pathways get enforced, and oversight bodies can ask for outputs on a timetable.
Three dates show how the contemporary U.S. model translates public interest into policy machinery.
First: the House Oversight UAP hearing (July 26, 2023) titled “Unidentified Anomalous Phenomena: Implications on National Security, Public Safety, and Government Transparency” held on July 26, 2023. Hearings matter less for what any one witness says and more for what they authorize institutionally: they put UAP on a formal oversight record, create incentives for agencies to respond in writing, and normalize follow-up questions about processes instead of anecdotes.
Second: the same day, July 26, 2023, The New York Times published an article reporting that a former national intelligence official told representatives the U.S. government is sheltering alien spacecraft. That allegation is not a policy mechanism. It is a public-attention accelerant, and attention is what turns oversight into sustained political energy instead of a one-off news cycle.
Third: the FY2024 NDAA signed into law on December 22, 2023. The NDAA (National Defense Authorization Act) is the annual defense-policy law that agencies plan around, comply with, and brief against. Whatever the public thinks “disclosure” should mean, the NDAA is where disclosure becomes enforceable expectations, because it can shape reporting requirements and compel recurring engagement from the defense establishment.
Inside that same institutional arc sits AARO (All-domain Anomaly Resolution Office), the dedicated U.S. office built to operationalize UAP handling as a standing mission rather than an ad hoc response.
AARO’s mandate framing is policy-first, not spectacle-first: it disseminates UAP reporting guidance for Department of Defense and intelligence personnel, and it works to resolve UAP reports that impact national security and personnel protection. Those two verbs, guidance and resolution, are what institutional disclosure looks like in practice. Guidance standardizes what personnel are supposed to do. Resolution forces the system to treat reports as something that must be closed out to a defensible endpoint, even when the answer is mundane.
The complication is that institutionalization produces credibility and constraints at the same time. Credibility rises because rules and offices create repeatability: oversight committees can demand briefings; agencies can point to published guidance; and reporting becomes less dependent on personal networks. Constraints rise because classification law and operational security set hard limits on what can be released publicly, even when oversight bodies are satisfied behind closed doors.
Politics also shapes messaging. Agencies have incentives to show competence, avoid revealing sensitive collection methods, and manage public expectations. Lawmakers have incentives to demonstrate accountability, signal seriousness to constituents, and differentiate themselves in a high-attention issue area. That interplay explains why the public-facing layer of “disclosure” often feels partial even when the institutional layer is expanding.
High-profile allegations sit on top of this machinery, not in place of it. David Grusch has been identified in reporting as a whistleblower who made claims about extraterrestrial life at a Congressional hearing, and those claims drove headlines. The durable signal, though, is whether systems exist that keep producing guidance, required reporting, and oversight engagement after the headline cycle ends.
Use a simple evaluative lens: ignore virality and look for durability. A real disclosure push leaves behind institutions (named offices with an assigned remit), mandated reporting (requirements that force recurring compliance), and auditable outputs (public guidance, formal reports, or oversight records that can be referenced later). Testimony can trigger attention, but institutions determine whether anything persists.
Applied to the Ecuador 2005 question raised earlier in this article, the strategic relevance is not that one government “got interested” early. It is whether the interest was converted into durable mechanisms that outlast personalities and news cycles. That is the standard modern disclosure has set: offices plus mandates plus oversight, constrained by classification, and shaped by politics.
That modern benchmark is also the most practical tool for judging what the CEIFO claim means in the near term: if the sources do not establish the unit’s existence, the only responsible move is to evaluate future claims by the same governance signals.
What CEIFO means for 2025 and 2026
Your edge in 2025 and 2026 is evaluation skill, not more headlines. For anyone tracking UFO sightings 2025 and UFO sightings 2026, the CEIFO story is useful less as a “lost file” narrative and more as a test: questions to ask when a government announces a UAP unit, does it signal real investigative capacity or pure PR?
The complication is structural: a state can look “serious” without releasing sensitive radar tracks, cockpit audio, or pilot identities. So you have to judge the scaffolding around the announcement, not the volume of clips circulating online.
Start with a hard limitation from the source set you have: none of the provided excerpts explicitly mention Ecuador’s CEIFO as a current government unit, and they do not state its present status (existing, renamed, merged, or dissolved). The excerpts that do use the acronym “CEIFO” point to a different entity tied to Stockholm, including an English expansion as “Centre for Research in International Migration and Ethnic Relations,” which underlines how easily acronym reuse can muddy claims if you do not anchor them to an official mandate and org chart.
A second limitation matters just as much for present-day signal-checking: the provided documents contain no Ecuador-government UAP or UFO statements from 2023 to 2026, meaning there is no source-backed trail of recent press briefings, FOIA-style releases, or parliamentary inquiries to evaluate.
Latin America does not need CEIFO verification to establish precedent: the Peruvian Air Force created O.I.F.A.A. in December 2001 and renders it in English as the “Office of Investigations of Anomalous Aerial Phenomena.” That date-stamped, named office is the baseline standard for what “real” looks like: an identifiable unit with a formal start point you can cite, not a vibe.
- Data types: What sensors and records are collected and retained? Radar, EO/IR video, ATC logs, maintenance data, meteorology, flight plans, chain-of-custody, and retention periods should be spelled out, or the “investigation” is just a mailbox.
- Investigative authority: Who can task analyses, request data, and compel cooperation? If the unit cannot pull primary records from air defense, civil aviation, and contractors, it cannot separate anomaly from artifact.
- Reporting pipeline: Who can report; how is triage handled; what protections exist for pilots and operators? safety protections, and a defined triage threshold (what gets elevated vs. closed) are the difference between safety reporting and stigma-driven silence.
- Transparency outputs: What is published (guidance, annual summaries, redacted cases) and on what cadence? A real program produces repeatable artifacts on a schedule, not one-off interviews.
- Oversight/appeals mechanisms: What is the equivalent of FOIA-style access, inspectors general, parliamentary committees, or independent review? Without a mechanism to challenge denials and audit process, “classified” becomes a permanent escape hatch.
Use one discipline and do not break it: unidentified does not mean unexplainable. “Alien disclosure” and “non-human intelligence” claims earn attention only after the prosaic categories are tested against the best available data: sensor error, misperception, balloons, drones, aircraft, atmospheric effects, spoofing, and classified human tech. Treat extraordinary conclusions as the last step in an elimination process, not the starting point.
Actionable takeaway: bookmark governance signals, not personalities or viral clips.
- Save the official mandate or founding order that defines scope and powers.
- Track org charts and named roles that show who owns triage and analysis.
- Archive reporting guidance (who can report, protections, required fields, retention).
- Log transparency outputs and cadence (summaries, redacted cases, methodology notes).
- Collect oversight references (FOIA-style routes, inspectors, committees, appeal paths).
A precedent hiding in the archives
The Ecuador-2005 CEIFO claim only matters as precedent if it can be anchored to primary documents, and the materials provided here do not substantiate CEIFO directly.
The verification gap and the acronym collision are the core constraint: without documentary proof, the story stays in the realm of assertion, not record. In practice, defense institutions treat anomalous aerial reports as airspace, safety, and security problems, which is why the burden of proof sits on traceable paperwork and auditable handling rather than anecdotes. That is also the same institutional logic the introduction set out: the claim is only as strong as the mandate, owning office, and paper trail you can actually point to, not the volume of reposts.
Use a publishable-output benchmark: FEMA’s official Public Assistance Program and Policy Guide exists in a Fourth Edition (Version 4), showing how a public program can publish sanitized methodology without exposing sensitive details.
The strongest proof would be CEIFO founding instruments, renewals, and ministry or org-chart references; allegations of a “government UFO cover-up” circulate in discourse but are not established by the supplied material. Track primary documents, publishable guidance, and archival releases next.
Frequently Asked Questions
-
What is CEIFO and what did Ecuador supposedly create in 2005?
The article describes a claim that Ecuador’s Defense Ministry created a formal UAP/UFO investigation capability in 2005 often referred to online as “CEIFO.” It emphasizes that this would be significant if proven because it would predate today’s disclosure wave by years.
-
Do the provided sources actually mention an Ecuadorian CEIFO UAP unit?
No-none of the provided source documents mention CEIFO by name in connection with Ecuador, a defense ministry, or UAPs/UFOs. The article states the documentation trail in the supplied materials is thin and does not substantiate the unit’s existence.
-
What does “CEIFO” mean in the sources cited in the article?
In the provided sources, “CEIFO” expands as “Centre for Research in International Migration and Ethnic Relations,” tied to Stockholm University. The article notes there is no Spanish-language expansion in the sources to cross-check an Ecuadorian government acronym.
-
Why would a defense ministry create a UAP reporting channel in 2005?
The article argues it would be operationally rational as an airspace safety and sovereignty function: unknown radar tracks and pilot safety reports require a formal intake and triage process. It also notes Ecuador received a modernized TPS-43 surveillance radar from the United States, and increased surveillance predictably increases the number of anomalies that must be reconciled.
-
What would a real defense UAP investigation unit look like on paper?
The article says credibility would come from a mandate, a named owning office, defined workflows, and retrievable records rather than dramatic claims. It lists a typical workflow: intake, triage, data capture, classification, resolution/closure, and archival with records retention.
-
What data and records should a credible UAP office collect and preserve?
The article says to expect pilot observations tied to flight data, radar tracks, ATC logs and audio, civilian statements routed through authorities, and photos/video with intact original metadata. It stresses chain of custody and multi-sensor corroboration (e.g., visual plus radar plus ATC audio) as key quality markers.
-
How can I evaluate new claims about an Ecuador CEIFO-style UAP unit in 2025-2026?
The article recommends ignoring virality and looking for durability signals: an official founding order/mandate, org charts with named roles, published reporting guidance, repeatable transparency outputs on a cadence, and oversight mechanisms (FOIA-style routes, inspectors, committees, appeals). It also gives a regional benchmark: Peru’s Air Force created O.I.F.A.A. in December 2001 (“Office of Investigations of Anomalous Aerial Phenomena”), which is a date-stamped, named office.