You keep seeing the same headline recycled across UFO news and UAP news: “a UFO shut down America’s nukes.” The claim is enormous, the clip-friendly certainty is intoxicating, and the sourcing is usually a fog of secondhand quotes, screenshots, and confident narrators who skip the paperwork.
The core anomaly is real in the sense that it is consistently summarized the same way in public-facing retellings: a 1967 Malmstrom Air Force Base weapons-system event in Montana, widely described as 10 Minuteman missiles going offline in rapid sequence and later linked in popular summaries to a UFO sighting. That pairing, nuclear readiness plus an alleged aerial intruder, is exactly why the story persists.
The friction is that repetition is not verification. The versions most people can access quickly do not, on their own, settle what caused the shutdown, how the failure propagated, or whether any UAP was involved at all. Even mainstream coverage tends to anchor the human vantage point rather than publish case-closing technical records: ABC News, for example, reported a witness was “monitoring the launch control center for 10” missiles at Malmstrom in March 1967.
That evidentiary gap matters more in the current disclosure climate, not less. AARO’s Historical Record work discusses historical nuclear-related UAP claims broadly and uses cautious language, attributing some extraordinary interpretations to misunderstanding rather than confirmed non-human activity. That posture forces a clean separation between what is alleged and what is demonstrated.
There is also a public paper-trail signal, even if it is not a mechanism: public-interest repositories list FOIA material described as pertaining to a March 16, 1967 Malmstrom-related incident.
This article separates the Malmstrom claim into three practical buckets: what is consistently claimed, what is anchored to accessible documentation, and what would qualify as case-changing evidence instead of another retelling.
To do that cleanly, you need two baselines: how a Minuteman missile flight was organized at Malmstrom, and what “No-Go” does and does not mean in that operational context.
Malmstrom, Minuteman, and Nuclear Readiness
A ten-missile shutdown at Malmstrom is not a trivial glitch because “10” maps to an operationally coherent unit: a missile Flight. In the 1967-era Minuteman organization described in the historical source set, a Malmstrom Flight consisted of 10 missiles, meaning reporting that “10 missiles” went No-Go is describing an entire managed set going unavailable, not an arbitrary count pulled from a wider field.
That unit framing gets even more specific in accounts that name Alpha Flight. Alpha Flight at Malmstrom is identified as equipped with 10 Minuteman IA missiles, an early Minuteman ICBM variant tied to Malmstrom’s initial deployments. So “10” is not just the number of affected silos, it matches the inventory of a named Flight in the reporting, which is why the phrase shows up so consistently.
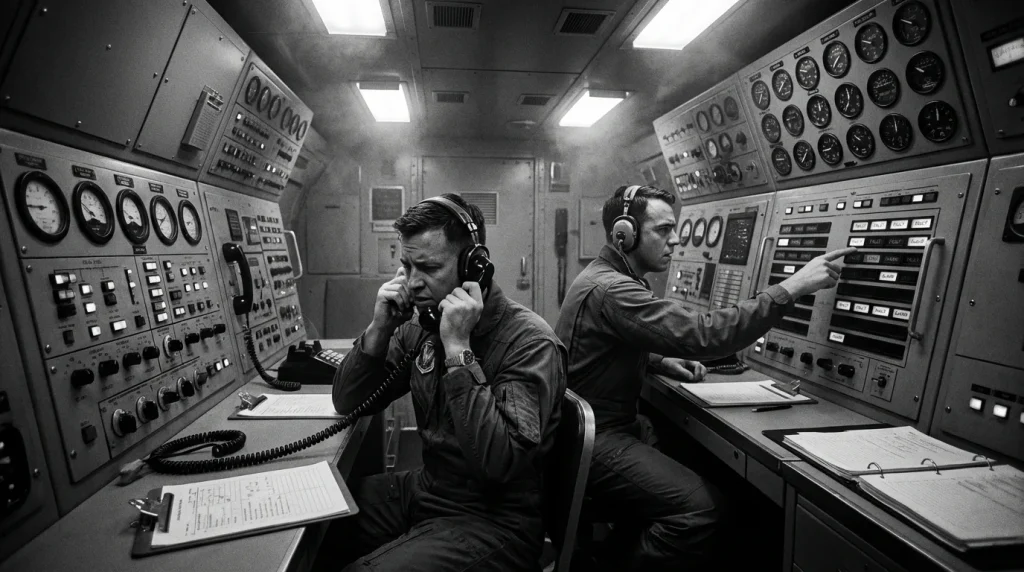
A Flight was not ten missiles sitting together on one pad. It was a distributed set of Launch Facilities (LFs), individual remote missile sites, tied back to a Launch Control Center (LCC), the underground command-and-monitoring node where crews oversaw status, communications, and control functions for their assigned facilities. That architecture is the baseline you need for the Malmstrom story: centralized monitoring and command logic at the LCC, with physically separated LFs spread across the countryside.
That distribution is the practical reason clustered failures attract attention. If ten separate LFs are geographically separated but administratively grouped under one LCC-managed Flight, then multiple rapid “No-Go” indications across those sites reads differently than a single-site fault. It signals a readiness problem at Flight scale, not a one-off maintenance discrepancy at a lone LF.
No-Go is a readiness status concept: it means the system is not in an acceptable condition to perform required mission function. It does not need to imply a dramatic physical event at a launch facility. It does mean the crew is seeing a condition serious enough, by checklist and technical criteria, that the missile or its associated support paths cannot be treated as available for the mission until the condition is cleared.
Strategic missile command-and-monitoring is built to avoid accidental or ambiguous outcomes, using redundancy and safety interlocks so that a single bad indication or single-point problem does not translate into unsafe behavior. The fact that the Department of Defense test and evaluation community maintains records assessing system performance and safety reflects how central safety engineering and controlled failure modes are to this mission area.
The disciplined way to read “ten No-Go” is not to jump to conclusions, but to ask structured questions that match how the system is organized: Is the unit of impact a Flight (ten missiles managed together)? Is the control node the LCC where common indications and procedures converge? Are the affected endpoints the distributed LFs where the missiles physically sit? And when someone says “No-Go,” are they describing an operational unavailability state, not an explosion, not a launch, and not a simple nuisance light?
Those framing questions matter because the 1967 Malmstrom accounts are not primarily about one broken component; they are about a flight-scale status change described as occurring within a short window.
What Happened During the 1967 Event
The 1967 Malmstrom narrative persists for one reason: it compresses into a clean sequence that feels causal. In the commonly repeated version, reports of an unusual light or object near launch facilities are followed by an internal escalation up command channels, and then a rapid shift of ten missiles to No-Go (non-mission-capable status). The “ten” matters because Alpha Flight is documented as a ten-missile unit, so a ten-missile status change reads like a single, discrete event rather than scattered, unrelated faults.
Later witness accounts, as they are typically retold, place security personnel at or near launch facilities describing a hovering object or a bright light near the site area. In these retellings, the security reports are treated as the first domino: the unusual aerial sighting is framed as close, localized, and time-adjacent to what operators later noticed inside the system.
Captain Robert Salas has publicly stated and testified that a red, glowing UFO was associated with ten Minuteman missiles going offline. That is his claim, and it is frequently presented as the central “eyewitness-to-system-effect” link in the overall story.
Public summaries generally compress the next step into “the report went up the chain,” without pinning down who held first-hand observation versus who received a relayed description. The friction here is practical: a security report can be direct observation by the reporting patrol, but the command-level awareness is often second-hand, moving through phones, radios, and message traffic that can preserve content while blurring timestamps and wording.
The event’s signature claim is near-simultaneity: ten missiles in the same flight are described as moving to a non-operational condition within a short window. Public summaries repeat this as a single flight-wide outage, which maps neatly onto the documented fact that Alpha Flight comprised ten Minuteman IA missiles. That structural fit is one reason the story reads as a unified incident rather than a cluster of routine, unrelated anomalies.
Repository descriptions are a different category of claim: they do not validate a UFO mechanism, but they do indicate that material about the incident is publicly cataloged. The Black Vault FOIA listings are described as referencing or requesting documents related to a March 16, 1967 missile-silo incident at Malmstrom. Treat that as an index of what requesters believe exists in government holdings, not as a conclusion about what caused the status changes.
Read the 1967 timeline like an investigator: track (a) who directly observed a light or object near a facility, (b) who only heard that description and passed it upward, and (c) which contemporaneous artifacts would lock down timestamps for the ten-missile flight event. The core gap is not storytelling detail; it is documentation detail. Until a reader can line up security reporting times, command notifications, and the exact moment each of the ten missiles transitioned status using dated records, the timeline remains compelling, but it stays a retelling rather than a time-synchronized reconstruction.
That missing synchronization is also why the case rises or falls on how testimony is sourced and labeled, not on how often the headline is repeated.
Witness Accounts and Public Testimony
The Malmstrom story persists because it is carried by narrated recollection: one person’s account of what they saw, another person’s account of what they were told, and later retellings that stitch those pieces into a single narrative. That structure matters because a testimony chain is elastic. It preserves the headline claim while allowing dates, distances, and even who witnessed what to drift as the story is repeated across decades.
This research set has a hard limitation: it does not include robust, citable service-record corroboration (rosters, AFSC verification, duty logs, unit records) for the best-known Malmstrom narrators. In this section, positions and on-shift roles are labeled as claimed unless they are directly anchored to a verifiable record.
The best-known “inside the capsule” narrator in public retellings is Robert Salas, commonly described as having been on a missile combat crew in an underground launch control center (LCC) during the March 1967 incident. In the versions circulated publicly, his first-hand layer is operational: alarm conditions, loss-of-status indications, communications, and the experience of being the person responsible for reporting and responding. The second-hand layer is the trigger story: what topside personnel said they were seeing near a facility, relayed down to the LCC by phone or radio. Without service-record anchors in this research set, Salas’s exact duty position and shift status must be treated as claimed even when repeated confidently in documentaries and interviews.
Another account type is the “outside the fence line” report: security personnel describing unusual lights or an object near a launch facility. In most public versions, these details enter the record indirectly, as statements relayed to LCC crew members and later repeated in interviews. The key methodological split is simple and decisive: “I observed a light/object at the site” is first-hand; “the guard told me they saw a light/object” is second-hand, even if the listener is otherwise a direct witness to the missile-status anomaly.
Books, lectures, and media packages amplify the story by selecting the most legible details and dropping the rest. That is why specifics diverge: later recollections tend to standardize the number of missiles, the sequence of calls, and the description of what was seen, while contemporaneous documentation would preserve messier, less cinematic uncertainty. This research set includes examples of what verifiable anchors look like in principle, such as a General Dynamics News notice documenting John Martinez’s service as a missile maintenance technician from January 1966 to January 1970, and an Air and Space Forces item identifying Capt. Robert E. Servant in a missile-crew context. Those anchors establish real-world personnel facts, but they do not, on their own, corroborate the UFO or shutdown claim.
Use a two-label rule and keep it consistent: treat “I saw X” differently from “I was told X,” and treat “decades-later recollection” differently from “contemporaneous log.” When you carry those labels forward, the Malmstrom narrative becomes easier to evaluate without either dismissing it outright or granting it evidentiary weight it has not earned.
Once those labels are in place, the question becomes practical: what technical signatures would have to exist for any proposed cause-mundane or extraordinary-to be more than a story.
Technical Theories and Alternative Explanations
When ten missiles flip to No-Go inside a tight window, the serious work is not picking the most dramatic story. It’s identifying which observations would discriminate among competing mechanisms. Investigators start by hunting for a common-mode failure, meaning one shared cause capable of triggering multiple faults across systems that are otherwise designed to fail independently, because that is the shortest path from “improbable” to “explainable.”
None of the provided source excerpts contain an identifiable, documented “official explanation” that attributes the Malmstrom 1967 ten-missile event to a specific technical mechanism. Some excerpts gesture at the existence of an “official explanation” without stating what it was, and a social media post’s “the military said…” line is an unverified claim without documentary backing in the excerpt. Treat any definitive “the Air Force concluded X caused it” statement as unverified unless the document and its technical content are actually shown.
Shared infrastructure and cascading faults are the first place to look because they naturally produce cluster behavior. A single upstream power quality event, a shared distribution point, a grounding problem, or a failure in common monitoring infrastructure can create multiple downstream “No-Go” indications nearly simultaneously, even if each missile’s internal health is unchanged.
Monitoring and communications artifacts can also create a “ten at once” appearance. If the reporting path is degraded, you can get synchronized status changes, delayed updates, or repeated fault annunciations that reflect the health of the link or the monitor, not ten independent equipment failures. This is exactly why engineering programs lean on defined go/no-go criteria derived from prior test data, and why development and acceptance cycles include functional logic testing, diagnostic troubleshooting, and go/no-go testing: the system must reliably distinguish “real fault” from “bad data path.”
Maintenance, test support equipment, and procedural interactions matter because routine actions can become a common-mode input. A maintenance evolution, a configuration change, a calibration step, a test set connection, or a checklist branch taken across a site can introduce a shared condition that drives multiple No-Go reports. The question is not “did maintenance happen,” but “what was touched, in what order, and what did the logs say before and after.”
EMI and EMC susceptibility is a real engineering domain with testable limits, not a catch-all. Military technical literature documents the development of interference and susceptibility limits and the techniques used to establish those limits, reinforcing that EMI claims are adjudicated with measurements against defined criteria rather than narrative alone.
The UAP hypothesis asserts an external, directed stimulus that drove multiple independent systems into an abnormal state. That is a higher evidentiary bar than any internal engineering failure family because it requires more than human recollection: it demands objective instrumentation showing time-correlated transients, fields, or signals consistent with a coupling path into the affected equipment, plus independent detections that establish the external source existed where and when it would need to operate.
Shared infrastructure or cascading fault gains strength if records show a common power transient, breaker operation, bus disturbance, grounding anomaly, or synchronized alarms across unrelated subsystems at the same timestamp. It weakens if independent, missile-specific fault histories appear with no shared upstream anomalies and no common time marker.
Monitoring or communications artifact gains strength if message traffic logs show dropouts, retries, corrupted frames, timebase issues, or a reporting node fault that could propagate a No-Go state broadly. It weakens if raw, local fault printouts at each unit match the central indications and show genuine equipment-level detections rather than a single-point reporting failure.
Maintenance, TSE, or procedural interaction gains strength if maintenance forms, configuration logs, and test-equipment records show a shared evolution within the window, especially if the No-Go onsets align with specific actions and clear when the action stops or is reversed. It weakens if the maintenance record is quiet, no shared configurations changed, and the failure signatures differ in ways inconsistent with one procedural trigger.
EMI/EMC mechanism (conventional) gains strength only with instrumentation: recorded power transient logs, measured field strengths, interference monitoring, equipment susceptibility evidence, and repeatable coupling paths tied to the site’s wiring and shielding. It weakens if there are no transient records, no anomalous measurements, and the fault patterns do not match known susceptibility behavior.
External UAP interference gains strength if independent sensors show correlated detections (radar tracks, optical records, electronic support measures), aligned in time with objective internal logs (fault printouts, power anomalies, timing disturbances) across multiple points, plus a physical mechanism consistent with the measured data. It weakens if the only evidence is retrospective testimony without synchronized technical artifacts.
Use an X/Y/Z filter when you read any new claim: X is missile-level fault truth, Y is shared-site common-mode context, and Z is external corroboration strong enough to justify an extraordinary mechanism.
- Collect time-correlated fault data (fault printouts, status histories, timestamps) for each affected unit and the central reporting path. (X)
- Pull power and grounding records (transient logs, breaker events, bus alarms) that can confirm or eliminate a shared upstream disturbance. (Y)
- Verify message traffic and comms diagnostics showing what the network and monitoring chain reported, not just the final No-Go state. (Y)
- Reconcile maintenance and test-equipment documentation (work orders, configurations, calibration logs) covering the exact window. (Y)
- Demand independent sensor correlations (radar and other detections) if any external-interference claim is being made. (Z)
If a “document dump” doesn’t include those categories, it won’t discriminate between common-mode engineering failures and extraordinary interference claims, and it won’t move the case.
Those standards also explain why the same handful of nuclear-linked stories recur: they come from environments that generate reports, but do not always release the instrumentation that would close the loop.
Why Nukes Keep Appearing in UAP Reports
Nuclear sites keep showing up in UAP narratives for structural reasons, not because they are inherently more “paranormal.” A missile wing or weapons storage complex runs on layered security, constant monitoring, and tightly managed access, so more people are watching more instrumentation more of the time. Those facilities also enforce strict reporting channels, which creates a paper trail whenever anything feels off, even if the root cause is mundane. Add the emotionally charged stakes of nuclear readiness and you get a setting where ambiguous events become memorable, retellable, and difficult to let go.
Malmstrom persists in later UAP disclosure discourse precisely because it is an unusually durable combination: nukes plus a system anomaly plus an unusual aerial report. Secondary summaries routinely cite it as nuclear-linked and fold it into broader “government cover-up” and “non-human intelligence” speculation, even when those later conclusions outrun what primary, contemporaneous documentation can support.
The loop is straightforward: partial visibility creates permanent interpretive room. National-security context limits what becomes public; later declassification is incomplete and uneven; and the remaining gaps invite confident storytelling. You can see the pressure for records in persistent document-seeking efforts through FOIA repositories, alongside the reality that multiple institutions maintain evaluative or historical holdings that may be relevant (DOTE performance and safety evaluations, Cold War legacy documentation programs, DTIC custody of Minuteman-related materials, and Air University Press historical analysis).
The friction point is how retellings accrete “evidence” as they spread. Some public retellings, especially on social media, layer in asserted photographs, landing traces, or electromagnetic disturbances. Treat those as claims that require sourcing, not baseline facts. The technical excerpts in this research set do not provide specific UAP-linked power-transient logs, maintenance-bench findings, EMI datasets, or radar tracks, so those additions cannot be treated as supported just because they are frequently repeated.
Patterns are not proof. They are prioritization signals. Use “nukes keep showing up” to demand better records and clearer chains of custody, not to declare conclusions, especially during attention spikes driven by trend coverage like UFO sightings 2025 and “UFO sightings 2026.”
- Separate what primary records actually show from what later summaries assert.
- Require a source for every upgraded claim (photos, traces, EM effects, radar), or treat it as unverified.
- Ask for the missing artifacts that would settle key disputes (logs, maintenance documentation, and authenticated sensor records), instead of letting the absence of evidence become evidence of anything.
What Malmstrom Still Demands We Answer
Malmstrom remains influential for a simple reason: the operational claim is concrete, while the causal claim is not settled in public documentation. Public summaries consistently point to a 1967 Malmstrom weapons-system anomaly involving 10 missiles, and later retellings attach that anomaly to UFO reports, but the key evidentiary details stay contested in public view.
The context section explained why “10” is not a throwaway number. It maps cleanly to a Flight sized operational unit, and clustered No-Go (non-mission-capable) status matters because it is a readiness event, not a spooky anecdote. Ten missiles failing inside a single operational envelope is the hook that keeps the story alive even when every other detail gets argued over.
The timeline and witness sections showed where the public case actually lives: attributed testimony, interviews, and retellings with uneven proximity to direct observation. Some accounts are close to the console and security response; others are several steps removed. That distance is where the narrative thickens, because each hop increases the chance that timing, wording, and “what was seen” drift from what was written down at the time.
The technical section tightened the standard of proof. Multiple conventional pathways can drive No-Go conditions, and electromagnetic threats are real, testable engineering concerns in military systems, not sci-fi. Extraordinary claims require discriminating artifacts like hard logs and correlated tracks, and no provided excerpt supplies a confirmed official causal mechanism, a named failure chain, or the underlying printouts that would let outsiders adjudicate competing explanations.
The policy section made the constraint explicit: disclosure mechanisms can expand the record, but classification and archival realities cap what emerges. Public pathways for potentially relevant records include FOIA repositories and document collections, plus institutional holdings that often surface through summaries and declassified releases, including Cold War archives and historical investigation files like Project Blue Book. Other likely custodians for adjacent material include legacy documentation programs and defense technical repositories.
Taken together, that brings you back to the same three-bucket sort from the introduction: the consistent public claim (ten missiles, rapid No-Go, reported aerial light/object), the limited set of accessible anchors, and the narrower set of artifacts that would actually change the case.
- Authenticated contemporaneous security reports describing an aerial object, with times, locations, and sign-offs.
- Fault and fault-history printouts from the affected sites showing specific codes, sequence, and resets.
- Command-post message traffic and alerting records tying field reports to higher headquarters in real time.
- Correlated sensor or radar data that aligns with the security timeline and the system anomaly.
Use that checklist to grade UFO news and UAP disclosure claims fast: prioritize contemporaneous records over memoirs, authenticated provenance over screenshots, and cross-correlation across independent systems over single-source storytelling.
Frequently Asked Questions
-
What happened at Malmstrom AFB in March 1967 with the Minuteman missiles?
Public-facing retellings consistently describe a weapons-system event where 10 Minuteman missiles at Malmstrom AFB went to “No-Go” (non-mission-capable) in a short window. Later summaries often link that shutdown to reports of an unusual light or object near launch facilities.
-
Why do people always say “10 missiles” were shut down at Malmstrom in 1967?
Because “10” matches the size of a Minuteman missile Flight in the 1967-era organization described in the article. Accounts commonly name Alpha Flight, identified as having 10 Minuteman IA missiles, so a 10-missile outage maps to a single flight-wide readiness event.
-
What does “No-Go” mean for Minuteman missiles in the Malmstrom story?
“No-Go” is a readiness status meaning the system is not in an acceptable condition to perform required mission function, so it is treated as unavailable until cleared. It does not, by itself, mean an explosion, a launch, or a dramatic physical event at a launch facility.
-
Was the 1967 Malmstrom missile shutdown officially confirmed to be caused by a UFO?
No-this article states the provided source excerpts do not contain a documented official explanation attributing the 10-missile event to a specific mechanism, UFO-related or otherwise. Claims like “the military said…” are described as unverified unless the actual document and technical content are shown.
-
What is Captain Robert Salas’s claim about the Malmstrom 1967 incident?
He has publicly stated and testified that a red, glowing UFO was associated with 10 Minuteman missiles going offline. The article emphasizes separating first-hand console observations (missile status indications) from second-hand reports relayed from topside security personnel.
-
What are the main conventional technical explanations the article says investigators should check first?
The article prioritizes common-mode causes such as shared infrastructure/cascading faults, monitoring or communications artifacts that can make “ten at once” appear, and maintenance/test-equipment/procedural interactions. It also notes EMI/EMC susceptibility is a testable engineering domain that requires measurements, not narrative.
-
What evidence should you look for to judge whether the Malmstrom shutdown was a common-mode failure or external interference?
The article’s checklist calls for time-correlated fault printouts for each affected unit, power/grounding transient and breaker/bus records, and message-traffic/comms diagnostics for the reporting chain. For any external-interference claim, it adds independent sensor correlations such as authenticated radar/optical/ESM detections aligned to the same timestamps.