Note: the 1980 Citizens Against UFO Secrecy v. NSA lawsuit anchors the dispute over NSA-held UFO material, but the auditable “239” responsive-documents count appears in later FOIA production metadata and FOIA logs rather than in a plainly dated 1980 court filing. See the NSA FOIA reading-room topic “UFO and Other Paranormal Information” and an independently posted 1992 NSA FOIA log that contains the phrase “239 UFO RELATED DOCUMENTS” for the specific instance of that count.
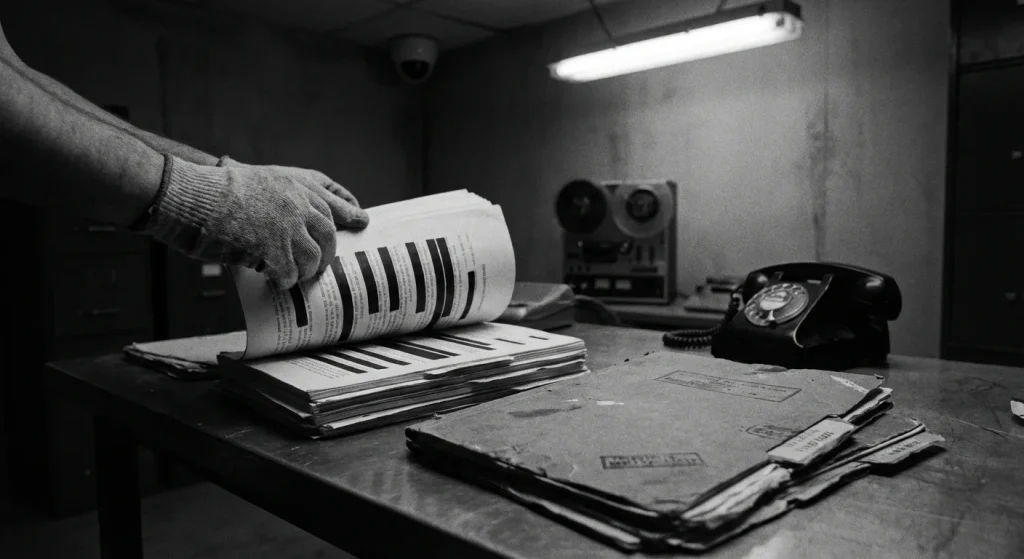
You have heard the pattern: “bombshell” UFO disclosure claims, confident threads, and recycled screenshots that never include the one thing that matters, a paper trail. The problem is not curiosity. The problem is receipts. If there is no docket number, no court caption, and no record of what an agency actually had to say under oath, you are not tracking disclosure. You are tracking storytelling.
One overlooked receipt exists, and it is not a rumor mill artifact. It is a court-captioned dispute that forced the National Security Agency into a formal posture and surfaced a hard number. In Citizens Against UFO Secrecy v. NSA, U.S. District Court for the District of Columbia (D.D.C.), Civil Action No. 80-1562, a 1980 Freedom of Information Act (FOIA) lawsuit put a dispute on the public record over NSA-held UFO related records. The precise, auditable “239 documents” count that circulates publicly appears in later FOIA production metadata and FOIA logs tied to that litigation rather than in a plainly dated 1980 court filing.
FOIA is the public’s leverage because it is the statute that lets you demand existing government records instead of trusting press-office summaries. The catch is that FOIA also bakes in secrecy tools that can preserve national-security silence even when a dispute reaches a judge. One of the sharpest is a Glomar response (neither confirm nor deny), a posture agencies use to protect even the fact of a record’s existence. In this litigation, the NSA used that posture, which tells you immediately why “they have files” and “you can read the files” are separate universes.
The core tension this case exposes is the one most UFO news and UAP news commentary skips: in FOIA litigation, records can be acknowledged or at least implicated through the act of fighting over them, yet still be withheld or gutted through FOIA exemptions and redactions. Existence can be placed on the record. Content can remain classified.
This article stays inside what is documentable: what the lawsuit’s paper trail shows, what “239 documents” can realistically mean, and what it does not establish. It will not claim this proves non-human intelligence, a crash-retrieval program, or any other alien disclosure narrative. You will leave with a working filter: existence on record does not equal disclosure of content.
To apply that filter, it helps to start with a basic question the internet rarely asks: why would the NSA have UFO-related material in the first place?
Why the NSA would have UFO records
If you expect the NSA to “investigate UFOs,” you will misread what an NSA file actually indicates.
The National Security Agency sits in the intelligence pipeline, not the adjudication seat. Its job is to collect and handle foreign intelligence derived from signals, then move that intelligence to decision-makers. Executive Order 12333 is the foundational authority describing NSA collection, retention, analysis, and dissemination of foreign signals intelligence. In other words: an NSA record usually signals an intelligence trail about communications, not a determination about what a craft was.
Signals intelligence (SIGINT), intercepted communications and electronic signals analyzed for national security, naturally scoops up references to unusual events when those events touch military operations, air defense, or diplomatic reporting. A pilot call, a radar operator’s report, a base-to-command alert, or a foreign military message about an “unknown track” is all communications. Those communications are collectible and reportable even if nobody inside the NSA is tasked to solve the underlying mystery.
That’s why the “UFO file” expectation breaks down. As set forth in EO 12333 and National Security Council Intelligence Directive 6 (NSCID-6), NSA collects, processes, analyzes, produces, and disseminates SIGINT. Those verbs describe an assembly line: acquisition, exploitation, analytic write-up, and distribution. If a UAP sighting triggers comms traffic, it can appear in NSA-held material as incident chatter, foreign reporting, or operational alerting, while the agency remains agnostic about what the object was.
The key distinction that fuels government cover-up narratives is straightforward: collecting or reporting communications about an incident is not the same thing as investigating the phenomenon. An intercepted message that mentions “unidentified” is evidence that somebody said it, not proof that the NSA concluded “non-human intelligence” is real.
Classification follows intelligence equities, not how exotic the topic sounds. A bland reference to “unidentified aircraft” can still reveal collection sources and methods, foreign targets, sensor coverage, analytic techniques, or what U.S. leaders were being briefed in real time. In foreign-intelligence work, context is often more sensitive than the headline.
That’s the nuance most people miss: secrecy alone does not validate extraordinary claims. A document can be withheld because it exposes how the U.S. learned something, not because it confirms what was seen.
Use a simple rule: “NSA has records” is a scope clue, not a verdict. It points you toward communications, tasking, reporting chains, and foreign-intelligence context around a sighting. It does not, by itself, tell you the object’s origin, whether anyone “solved” the incident, or whether the government reached a conclusion beyond “this was reported and mattered operationally.”
Once you separate collection from conclusion, the 1980 case becomes easier to read for what it is: a fight over records and process, not a public release of answers.
Inside the 1980 FOIA lawsuit
The most important “UFO disclosure” detail here is procedural: the lawsuit forced positions and counts into the record, not revelations.
Primary-source citation (example locator):
- (a) NSA reading-room document title: “UFO and Other Paranormal Information” (NSA FOIA topic page).
- (b) Direct URL to a FOIA log where the “239” phrase appears: GovernmentAttic, “NSA FOIA Logs 1992” PDF, Governmentattic.
- (c) Verbatim quote of the line showing “239”: “239 UFO RELATED DOCUMENTS”.
- (d) Locator guidance: searchable GovernmentAttic PDF titled “NSA FOIA Logs 1992” contains the entry; use the PDF text search for the exact phrase “239 UFO RELATED DOCUMENTS” to find the line quickly. See the NSA FOIA topic page above for the reading-room context.
- Request records under FOIA: FOIA starts with a written request, and the statute sets the baseline expectation that an agency makes an initial determination within 20 working days (excluding weekends and legal holidays). That clock is what turns “silence” or “no records” into a reviewable event, rather than an indefinite stall.
- Receive an agency posture: release, withhold, or refuse to confirm: For national-security agencies, the practical early fork is simple: disclose something, withhold under exemptions, or issue a Glomar response when even acknowledging existence would itself reveal protected information. This is where FOIA Exemption 1 (properly classified national security information) and FOIA Exemption 3 (information barred from disclosure by another federal statute) matter, because they preserve secrecy even when the requester is clearly entitled to an answer.
- Escalate through the administrative process: FOIA’s built-in escalation is the administrative appeal: a requester can appeal after a denial or after the agency fails to issue a timely determination. That appeal record becomes the foundation for court review, because it pins down what the agency did and did not decide.
- File suit in federal court to force a defensible record: Citizens Against UFO Secrecy v. NSA is the precise lawsuit that turns a disputed request into a court-supervised paper trail: U.S. District Court for the District of Columbia (D.D.C.), Civil Action No. 80-1562. Once the case is docketed, the agency has to justify its position in a format the judge can evaluate, rather than relying on bare assertions.
- Litigate with declarations, orders, and FOIA-specific justification tools: The NSA’s own FOIA and declassification materials point back to a “memorandum and order” tied to Citizens Against UFO Secrecy, reflecting that the dispute produced formal court paperwork rather than informal back-and-forth. That is the core value of FOIA litigation: it compels sworn positions and judicially reviewable reasoning.
- Watch where the “239 responsive documents” claim becomes checkable: The 1980 lawsuit established the litigation anchor and the administrative case history, but the auditable “239” responsive-documents count appears in later FOIA production metadata and FOIA logs associated with the case. For example, the phrase “239 UFO RELATED DOCUMENTS” is recorded in a 1992 NSA FOIA log posted by GovernmentAttic, and the NSA reading-room topic for UFO material provides the agency context for related FOIA activity. The production metadata that is often cited alongside that count shows an NSA approval-for-release date of 11-12-2015 under later FOIA handling tied to the litigation history, which is why the public “239” trace is best understood as a later, auditable FOIA production artifact rather than a simple line in a 1980 docket filing.
FOIA litigation forces an agency to say, in a way a court can manage, what it searched for, what it located, and what it is withholding. It does not force an intelligence agency to declassify. NSA explicitly frames its withholding posture around FOIA exemptions 1 through 7, and it states exemptions 8 and 9 do not pertain to its missions. The result is predictable: the public can learn “records exist” and still learn almost nothing about what those records say.
Exemption 1 does the heavy lifting when the dispute touches classified national security information. A court can require the government to defend classification claims, but the remedy is usually procedural: better explanations, clearer categories, and confirmation of counts. Exemption 3 is even more structurally limiting because it is not a balancing test. When another federal statute forbids disclosure, Exemption 3 blocks release regardless of public interest or curiosity.
This is where a Vaughn index becomes the central litigation artifact. It is the document-by-document or category index that lets the government justify withholdings without disclosing the withheld information itself, and DOJ guidance requires that it reflect, for each item, that any reasonably segregable information has been released. That segregability requirement is real, but it is not magical: if the non-exempt fragments are trivial, you still get a “partial release” that carries very little substance.
Glomar fits into the same architecture. Even if litigation pressure makes the government commit to a position, that position can still be “we can’t confirm or deny,” and the court fight shifts from “show me the documents” to “is the refusal to acknowledge existence itself justified under the exemptions.” That is how FOIA can produce a public record full of counts, case numbers, and sworn declarations while leaving the underlying narrative locked away.
Use the litigation artifacts the way the judge does. Counts and search descriptions tell you what exists in some form; declarations tell you what the agency is willing to swear to; a Vaughn index tells you the shape of what is withheld and why. What you generally cannot infer, even from a clean “239 responsive documents” number, is the substance of the withheld material, because Exemption 1 and Exemption 3 are designed to preserve secrets even after a case forces acknowledgement.
That limitation is exactly why the next question is about structure: if you have 239 responsive items, what kinds of documents tend to make up a number like that inside NSA workflows?
What 239 documents might include
A classified cache can be large and mundane at the same time; quantity does not equal proof of non-human intelligence. “239 documents” is best read as a count of records that fit normal NSA workflows and retention rules, where many items are operationally sensitive by default even if they contain nothing exotic.
A plausible core of any NSA-held set is routine operational reporting: message traffic and teletype-style communications, serialized SIGINT reports, and watch-style updates written for fast dissemination. In the 1970s to 1980s reporting context, NSA SIGINT reports used standardized cover sheets and conspicuous classification markings; historic labels sometimes seen in archival material include “SECRET SAVIN” and “TOP SECRET TRINE.” Those markings matter because they reflect handling compartments and dissemination rules, not subject matter. These are era-accurate examples that may or may not appear in the specific 239-document set; see archival policy material and examples of historical NSA capture logs for context (NSA policy manual) and an archival capture document collection at GovernmentAttic (example).
Within that same ecosystem, TACREP (tactical SIGINT report) is a known reporting term, which makes “tactical” items a plausible type in any mixed bundle of NSA records. Tactical formats exist because commanders need time-sensitive fragments quickly, even when the underlying collection remains highly protected. For doctrinal and manual context about tactical reporting and DoD intelligence collection rules, see DoD Manual 5240.01 (DoD manual).
Another plausible bucket is technical or cryptologic analysis notes: brief write-ups explaining why a signal was assessed a certain way, what processing was applied, or which technical assumptions were used. These can be far shorter than narrative reports while remaining more sensitive, because they expose analytic tradecraft. Even a one-page note that references timing, direction-finding concepts, or targeting heuristics can reveal sources and methods far more directly than a longer summary.
Era-accurate context helps here without proving anything about the specific cache: CSIGINT reporting was organized by levels or echelons, with field site reporting described as “first echelon.” That structure naturally produces layers of paperwork: field-originated snippets, intermediate roll-ups, and higher-level summaries that repackage the same underlying events for different consumers.
Large counts also come from coordination artifacts that exist to move intelligence safely: liaison exchanges, inter-office memoranda, dissemination notices, and briefings prepared for cleared recipients. NSA reporting was routinely disseminated to senior military recipients under controlled channels, and that dissemination itself creates records: cover notes, distribution lists, and acknowledgement traffic. None of that implies extraordinary content; it implies a product moved beyond a single desk.
The least intuitive category is often the most common: internal routing and tracking. Routing slips, briefing sheets, and indexes or logs look administrative, but they can remain classified because metadata is intelligence. A subject line, an office symbol, a target nickname, a date-time group, or a distribution list can expose what was collected, when it was collected, and which units cared enough to read it.
This is also where “239 documents” can hide a lot of bulk. Case management procedures in the referenced record set specify how analysts are assigned and what data is logged, and they describe notification to program areas. Procedures like that exist to make work auditable and repeatable, and they naturally generate logs and indexes as standalone records. If those logs reveal targets, tasking patterns, or analytic ownership, they stay sensitive even when the underlying narrative is unremarkable.
Heavy redactions and withholdings create a story-shaped void: readers see counts, titles, and black bars, then supply their own plot. The problem is that classification is driven by exposure risk, not by how surprising the content feels to the public. A page can be withheld because it lists a field site’s reporting chain, references a compartmented marking like “SECRET SAVIN” or “TOP SECRET TRINE,” or reveals first-echelon sourcing, even if the substantive claim is mundane.
If the goal is to move beyond inference, the useful question is what kinds of material would actually let an outside reader evaluate an event instead of projecting meaning into redactions.
- Direct technical measurements that can be independently evaluated (instrument parameters, calibrated sensor outputs, reproducible signal characteristics).
- Corroborated source chains that show collection origin, processing steps, and analytic handling without gaps that invite storytelling.
- Cross-agency confirmations where separate systems report the same event with consistent timing and identifiers.
- Clear provenance metadata (serial numbers, dissemination records, and indexing that ties documents to a coherent timeline rather than isolated pages).
How this fits today’s disclosure fight
Modern ‘UFO disclosure’ is now being fought through institutions and statutes, not just anecdotes.
The through-line back to the 1980 NSA FOIA fight is structural: the public record expands when process forces agencies to search, account, and justify, but national security secrecy still sets hard limits on what can be released. Courts and FOIA mechanics can compel rigor and documentation without compelling the government to publish genuinely classified sources, methods, or operational details. That same tension is now playing out in a more formal governance ecosystem built to receive claims, investigate them, and publish what can be published.
The Department of Defense established the All-domain Anomaly Resolution Office, and AARO provides a central intake and investigative function. See AARO’s official site Aaro and the DoD establishment memo “ESTABLISHMENT, RESOURCING, AND LEADERSHIP OF THE ALL-DOMAIN ANOMALY RESOLUTION OFFICE” (DoD memo PDF).
Since 1980, the biggest governance upgrade is that “disclosure” is no longer just a fight over individual requests. The FY2024 NDAA includes provisions creating an “Unidentified Anomalous Phenomena Records Collection” at the National Archives. See the enacted FY2024 National Defense Authorization Act, Public Law 118-31 (PLAW-118publ31 PDF). The law instructs creation of an Unidentified Anomalous Phenomena Records Collection at NARA; quoted phrase: “Unidentified Anomalous Phenomena Records Collection” (Senate amendment text).
Congress has also made UAP oversight legible in a way that is hard to hand-wave away. The House Committee on Oversight announced and held hearings on these topics. See the committee announcement and hearing page for the Nov. 13, 2024 joint subcommittee hearing, “Unidentified Anomalous Phenomena: Exposing the Truth” (announcement) and (hearing page). The committee also listed a hearing titled “Restoring Public Trust Through UAP Transparency and Whistleblower Protection” for Sept. 9, 2025; that hearing is scheduled as of Sept. 9, 2025 per committee materials (announcement) and (hearing page).
Track the things that produce checkable outputs: the Sept. 9, 2025 House Oversight hearing record (scheduled as of Sept. 9, 2025), the mandated reports tied to AARO’s mission and the Historical Record Report, and the NARA mechanisms required under the FY2024 NDAA provisions. If those artifacts appear on schedule, with clear scope and documented sourcing decisions, the public record is expanding the same way it did in earlier FOIA fights: through process, not hype.
That emphasis on process only helps if you can verify what exists and submit requests that produce clean, reviewable outcomes.
How to verify and request records
Verification beats virality: you can check the record trail yourself. The strongest claims in the NSA-UFO paper trail are the ones you can tie to primary artifacts: an agency reading-room release, a FOIA case number, or a court caption that exists on a docket. Those artifacts come from the same systems that created the trail in the first place, which means you can verify them directly instead of relying on UFO news summaries that blur dates, agencies, and document status.
Agency release channels: start with the NSA’s FOIA Reading Room and FOIA submission portal, because the NSA itself hosts litigation-linked materials and release metadata for some records tied to Citizens Against UFO Secrecy. See the NSA FOIA topic page “UFO and Other Paranormal Information” (NSA FOIA).
NARA archives: use the National Archives’ Electronic Reading Room and FOIA pages when you need to separate what NARA treats as Operational records versus Archival records. That distinction determines whether you are requesting access to historically accessioned holdings or asking an agency to search active systems.
Secondary FOIA libraries: GovernmentAttic.org is a discovery tool because it publishes FOIA-obtained records and identifies the source agency for each document. Use it to generate leads, then verify provenance by matching stamps, case numbers, and release markings back to the originating agency. Example: GovernmentAttic posting of NSA FOIA logs (NSA FOIA Logs 1992).
Court records and dockets: confirm the exact caption and civil number before you assume any filing exists. DOJ reporting and listings can corroborate that Citizens Against UFO Secrecy v. NSA appears in D.D.C. as civil action 80-1562, which you can then track in PACER or archival docket sources.
A FOIA request must be in writing and must reasonably describe the records sought, and you submit it to the agency’s FOIA Office. “Reasonably describe” is operational: constrain the search so a FOIA analyst can actually run it. Use a tight date range, a specific subject line phrasing, named offices (if known), and explicit record types (for example: correspondence, memoranda, routing slips, indices, or final reports). Ask for releasable portions, and request that the agency process segregable material rather than holding the entire record back.
Delays are normal, but agencies still owe a timely initial determination under the statute (with statutory caveats). The outcome codes matter more than the wait:
- Glomar response (neither confirm nor deny): the agency will not acknowledge whether responsive records exist.
- Partial release/redactions: pages exist; the black bars show what was withheld, not what was searched.
- No records: a search was conducted and found nothing responsive as framed.
- Referral: another agency is treated as the proper holder for some pages.
A Vaughn index is the tool that forces clarity when withholding is contested: it should identify, by document or category, what was withheld and confirm that reasonably segregable information was released.
An administrative appeal is your first escalation after a denial, a Glomar response, heavy redactions, or even a failure to issue a timely determination. Many agency rules impose a 90-day window from an adverse determination, so treat the clock as part of your workflow.
Mandatory Declassification Review (MDR) is a distinct pathway aimed at classified information decisions, not general “any record” retrieval, and it is often the better fit when you can name the document and you are challenging classification rather than search adequacy.
- Anchor one claim to a primary artifact: an NSA reading-room item, a FOIA case number, or the 80-1562 caption.
- Cross-check your UFO sightings timeline against release dates using a simple rule: proximity is not causation.
- Draft a narrow FOIA request with a date range, record type, and precise subject line wording.
- Log the outcome code (Glomar, partial, no records, referral) and preserve the response letter as evidence.
- Appeal promptly when the reasoning is contestable or the determination is overdue.
| Timeline move | What you verify | What you do not claim |
|---|---|---|
| “UFO sightings 2025” spike | Release date and originating agency | That the release caused sightings |
| “UFO sightings 2026” spike | Whether new pages were actually posted | That sightings prove the content true |
| Old case reference resurfaces | Docket caption and civil number match | That the case proves a cover-up by itself |
What the NSA cache really proves
The NSA cache proves a narrow, bounded point: UFO-related records were treated as sensitive enough to trigger withholding and NCND behavior, but it does not prove non-human intelligence.
The lawsuit section showed why FOIA fights produce partial visibility: exemptions and tools like a Vaughn index force the government to describe what it is withholding and on what basis, without conceding the underlying substance.
The NSA-mission section sharpened the key constraint: NSA collection generates signals and intercept-derived records, not an investigative conclusion about what a sighting was.
The “239 documents” section put a hard guardrail on interpretation: a document count and classification posture can still be mundane, and category labels are not content claims. The specific auditable instance of the “239” phrasing appears in later FOIA production logs and metadata (see GovernmentAttic FOIA log) rather than as a plainly dated line in a 1980 docket filing.
The modern section closed the loop by anchoring disclosure in scheduled, mandated accountability points rather than open-ended lore.
Weight process artifacts over narratives: sourced documents with provenance, on-the-record filings, explicit exemption justifications, and verbatim hearing and report text beat screenshots, secondhand summaries, and numerology. That is the same paper-trail standard the introduction demanded: captions, docketable disputes, and controlled releases rather than recycled claims.
Watch the scheduled House Oversight hearing, “Restoring Public Trust Through UAP Transparency and Whistleblower Protection,” on Sept. 9, 2025, plus the ongoing AARO Historical Record Report and NARA-related mechanisms; and treat “239” with care, because “239 responsive documents” is not the same thing as “239” showing up as a page number or metadata in unrelated PDFs.
If you want a clean audit trail as this unfolds, follow the primary-source releases and the official hearing record, not the recycled takes.
Frequently Asked Questions
-
What was Citizens Against UFO Secrecy v. NSA (Civil Action No. 80-1562) about?
It was a 1980 Freedom of Information Act (FOIA) lawsuit filed in the U.S. District Court for the District of Columbia (D.D.C.) against the National Security Agency. The case forced the NSA into a formal, court-supervised record about what it searched for and what it would withhold.
-
How many UFO-related documents did the NSA acknowledge in the 1980 FOIA lawsuit?
The paper trail reflects a count of 239 responsive documents connected to NSA-held UFO-related records. The number appears in released NSA material in a tracked production context (including “BATES NO 101”) with an NSA approval-for-release date of 11-12-2015 under FOIA Case #78137.
-
What is a Glomar response and how did it affect the NSA UFO records dispute?
A Glomar response is when an agency will “neither confirm nor deny” the existence of responsive records. In this dispute, that posture illustrates how FOIA can put process and counts into the public record while keeping the underlying content out of reach.
-
Which FOIA exemptions most often keep NSA UFO/UAP documents classified?
The article highlights FOIA Exemption 1 (properly classified national security information) and Exemption 3 (information barred from disclosure by another federal statute) as the main barriers. These exemptions can justify withholding even when a case reaches a judge.
-
Why would the NSA have UFO or UAP records if it doesn’t investigate UFOs?
The NSA sits in the signals intelligence (SIGINT) pipeline, so it can collect and handle communications that mention “unknown” tracks or unusual events tied to military operations, air defense, or diplomacy. Having records indicates an intelligence trail about communications, not an agency conclusion about what the object was.
-
What kinds of documents could be included in the NSA’s “239 responsive documents” count?
The article says the count could include routine message traffic, serialized SIGINT reports, watch updates, TACREP-style tactical items, cryptologic analysis notes, dissemination records, and internal routing/tracking logs. It also notes historic classification markings like “SECRET SAVIN” and “TOP SECRET TRINE” that reflect handling compartments, not proof of exotic content.
-
How can you verify or request NSA UFO/UAP records without relying on screenshots or rumors?
Use primary artifacts such as an NSA FOIA Reading Room release, a FOIA case number (like #78137), or the court caption and civil number (D.D.C. 80-1562) and confirm them via agency portals or dockets (e.g., PACER). When filing FOIA, narrow the request with a date range, record types, and specific subject wording, and track outcomes like Glomar, partial release/redactions, no records, or referral.