A major reason UAP disclosure keeps stalling is structural, and it started earlier than most people think. If you follow UFO news for more than a month, the pattern becomes predictable: a grainy cockpit clip goes viral, a partial briefing leaks, officials deny a specific claim, and someone else insists that denial proves a cover-up. The loop leaves you with a worse problem than “What was that object?” You cannot tell whether secrecy is a plot or a system.
That tension sits under almost every argument about Unidentified Aerial Phenomena (UAP), meaning reported airborne objects or events that observers cannot immediately identify and therefore get routed into investigative and intelligence channels instead of public explanation. Is the silence evidence of non-human intelligence being suppressed, or is it the normal result of national-security information control doing what it is designed to do?
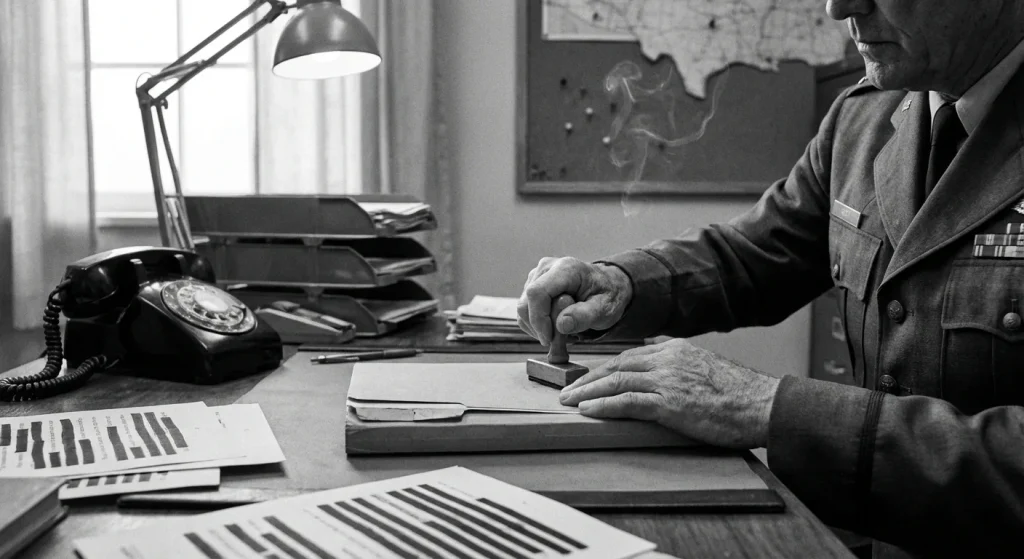
Here’s the core claim: a dry 1953 Air Force regulation still shapes today’s UFO disclosure and UAP disclosure arguments because it normalized centralized handling and a controlled public narrative. Air Force Regulation 200-2, titled “Unidentified Flying Objects Reporting,” was issued on 26 August 1953, received Change 200-2a on 2 November 1953, and exists in a later dated version on 12 August 1954. Those dates matter because they mark institutional design choices: who gets to speak, where reports consolidate, and how quickly ambiguity becomes “sensitive” by default. That architecture outlives any single incident, administration, or headline.
The modern continuity point is not a claim about outcomes. It is proof the machinery still exists. The all-domain anomaly resolution office (AARO), a Department of Defense office created to serve as the DoD focal point for UAP-related activities, was established by DoD memorandum dated July 20, 2022, and it produces the kind of bureaucratic artifacts systems produce, including a mission brief file titled “AARO_Mission_Brief_2025.pdf.”
This article resolves one tradeoff: the public’s demand for transparency versus the air-defense and intelligence constraints that make control, not openness, the default setting. You will leave with a framework for evaluating government UFO cover-up claims and UAP disclosure updates by asking what information system produced them, not just what the latest clip seems to show.
Cold War logic behind secrecy
In 1953, an ‘unidentified’ report was operationally indistinguishable from an intrusion until proven otherwise. The Air Force was living in the radar era, where a fast-moving blip on a scope could represent a navigation error, a misread, or an aircraft testing defenses, and the penalty for guessing wrong had become nuclear-scale. Strategic bomber doctrine treated long-range bombers as the delivery system that mattered most, which meant “unidentified aircraft” was not a curiosity category; it sat inside the same warning-and-assessment pipeline as any other potential penetration.
The complication was that better detection created more noise. Radar expanded what could be “seen,” civilians looked up more often, and every headline about unusual lights trained more people to report ambiguous stimuli. In that environment, mass reporting was not just inconvenient; it created a vulnerability. Flood the system with questionable reports and you consume the attention of controllers, intelligence officers, and intercept assets that were supposed to stay available for actual threats. Add nuclear anxiety to the mix and the Air Force also had to treat public panic as an operational factor, because panic amplifies false reports, crowds channels, and pressures commanders into rushed decisions.
The takeaway is simple: in 1952 to 1953, “unknowns” were handled as an air-defense and intelligence workload because the threat model demanded it, not because the subject was culturally entertaining.
AFR 200-2 did not appear in a vacuum; it formalized work the Air Force had already been doing for years. Project Sign ran from December 1947 to February 1949 and investigated 243 sightings, a volume that forced the institution to treat reports as casework rather than rumor. That initial push scaled down and transitioned into Project Grudge, reflecting a move toward tighter control and more routine handling of incoming reports rather than open-ended exploration.
By 1952, the Air Force shifted again by beginning Project Blue Book, a standing investigative program designed to centralize UFO case intake, evaluation, and recordkeeping because ad hoc responses were no longer compatible with the tempo of Cold War reporting. The point of that continuity is institutional, not sensational: once you create a process to receive, triage, and archive “unidentified aircraft” reports, you inevitably need rules that define jurisdiction, thresholds, and what counts as actionable information.
The clearest signal that UFO reporting had become a national-security information problem came in January 1953, when the Robertson Panel convened as a scientific advisory body asked to review UFO materials through a security lens. Its review did not stop at written summaries; the panel report included analysis of motion-picture films of sightings at Tremonton, Utah, dated 2 July 1952, which shows the government was assessing what kinds of evidence could drive public belief and operational workload.
The complication was not just what the objects were, but what the reporting ecosystem did to the defense system. If attention could be pulled toward the ambiguous, then attention itself became something to manage. A mature air-defense posture depends on disciplined signals, credible reporting, and clear authority over interpretation; uncontrolled fascination produces the opposite.
That logic is exactly why a formal regulation existed. AFR 200-2 framed Air Force interest as twofold: a possible national security threat and scientific or other interest. By 1953, codifying procedures was inevitable, and the era’s secrecy reads as a predictable response to threat perception and information overload, not as proof of any single hidden conclusion.
Those pressures-defense urgency, reporting volume, and public sensitivity-are the backdrop for what AFR 200-2 actually put into writing. The regulation matters less for any one case than for the rules it set on who reports what, and what the public is allowed to hear.
What AFR 200-2 actually required
AFR 200-2 mattered because it turned ad hoc UFO handling into enforceable procedure: an Air Force Regulation, not a one-off investigation, that set official procedures for handling UFO reports and the related flow of public information. At a systems level, the point was administrative control. AFR 200-2 established procedures for reporting information and evidence pertaining to unidentified flying objects, and it applied to all Air Force activities, meaning the same rulebook governed how a pilot’s sighting, a radar track, or recovered material would be treated across commands rather than being handled as a purely local curiosity.
That scope created a practical tension that still shows up in “official” statements. Procedures reward clean dispositions and disciplined communication. Public interest rewards raw, unresolved detail. AFR 200-2 sits directly on that fault line: it formalized how information moved inside the institution and what kinds of conclusions were safe to say out loud.
AFR 200-2 also assigned responsibilities connected to reporting, interception, identification, and air search as they relate to UFO events. The operational implication is straightforward: a “UFO report” under the regulation is not merely a story for historians; it is treated as an event category that can trigger real-world actions, tasking, and documentation.
AFR 200-2 did not leave “UFO” to popular imagination. It included a definition of “UFO” that is commonly cited as paragraph 2c in secondary discussions, but the only responsible way to quote or paraphrase it is to verify the exact wording and paragraphing directly from the primary regulation text first. That verification step is not pedantry; it determines what cases count as “unidentified” versus “identified” or “insufficient data,” and that boundary controls what gets escalated, investigated, or closed out.
Definitions matter operationally because they convert ambiguous observations into a standardized category that can be processed. A pilot describing lights with no reference points and a radar operator reporting an anomalous return can be very different events, but a regulation-level definition forces both into the same administrative question: does this meet the threshold for a UFO report under AFR 200-2? Once that threshold is met, the institution has permission, and in practice an expectation, to handle it through a prescribed procedure instead of improvisation.
The friction is that formal definitions optimize for consistency, not completeness. The public often wants the messy middle: partial data, contested interpretations, and unresolved possibilities. A regulatory definition, by design, narrows what “counts,” which can make the external record look cleaner than the underlying stream of observations.
AFR 200-2 shaped what could be discussed publicly by explicitly permitting a particular kind of disclosure. The regulation states, in the media-communication provision, that information may be furnished to news media representatives when an object “is positively identified as a familiar object” (see paragraph 9 of AFR 200-2). This quoted condition functions as a release gate that ties permissive public communication to a specific resolved condition rather than to ongoing uncertainty (AFR 200-2, Aug 26, 1953; see primary text).
Minimal classification context is enough to explain why this matters. Even without invoking the full architecture of classification law, Air Force activities routinely handle information that becomes constrained the moment it intersects capabilities, sources, or operational details. A rule that only clearly green-lights media engagement after positive identification naturally favors public statements that close cases out, and it discourages detailed public discussion while identification is uncertain.
The actionable way to read any “official UFO statement” in this framework is to ask one question first: did the institution positively identify the object as a familiar object, or is it still in an uncertain category? Under AFR 200-2’s release gate logic, that distinction predicts how much can be said, how confidently, and how quickly.
The supplied research packet lacks the AFR 200-2 pipeline specifics and cannot be used to reconstruct routing, form numbers, or message precedence. Treat AFR 200-2 as the instrument that established system-level procedures and the public-release gate, but do not infer exact routing or deadlines from unrelated excerpts.
One concrete example from the primary regulation is the report format it prescribes: AFR 200-2 requires numbered report items describing the object and incident, including identification number, altitude, heading, speed, home station, time and date (reported in Zulu time), and descriptive elements such as shape and size compared to known objects. That procedural language appears in the AFR 200-2 report format and should be cited directly when reconstructing reporting mechanics (AFR 200-2, Aug 26, 1953; see primary text).
Even without the missing pipeline mechanics, the regulation’s release gate and centralized control are enough to explain why secrecy can look intentional from the outside. Once an institution is built to speak clearly only after it has “resolved” a case, the unresolved cases become the quiet space where cover-up narratives thrive.
How a rule becomes a cover story
Secrecy often emerges from process design, not villainy. AFR 200-2 worked like a routing and release framework: it centralized how reports moved, who could speak, and what got cleared for public consumption. That structure alone can generate “government UFO cover-up” optics even if nobody coordinates a conspiracy.
The non-obvious part is that the same controls meant to prevent bad information from leaking also suppress the normal signals the public uses to judge good-faith work: timelines, raw data, intermediate hypotheses, and uncertainty. When you only see the final, sanitized answer, every delay and every missing document reads like intent instead of friction.
Three mechanisms drive that friction. First, bottlenecks: centralized routing concentrates authority. The more decisions that require a single office’s review, the more delay becomes normal, and the more “no comment” becomes the default. Second, incentives: in a system judged on closure, “identify fast” becomes the path of least resistance, while ambiguity becomes a non-public internal state. Third, information asymmetry: the public sees a stream of neat identifications, while unresolved cases are summarized thinly or not at all, creating a distorted distribution that feels curated.
Project Blue Book’s own archive reports 12,618 sightings or events compiled between 1952 and 1969. That volume forces triage. You do not process thousands of heterogeneous reports with bespoke write-ups, open-ended investigations, and fully declassified attachments; you build templates, standard language, and a pipeline that closes cases efficiently.
That is where “bottlenecks” become policy in practice. Centralized routing makes sense for consistency, but it also concentrates queueing. When every field report must be normalized, compared, and dispositioned through a narrow channel, delays become structural. The public experience is predictable: an incident happens, details go quiet, and an answer arrives later with fewer specifics than the initial rumor contained.
Blue Book also shows why bureaucracies categorize. Outcomes were tracked in buckets like identified, insufficient data (often labeled “insufficient information”), and unknowns. The official Project Blue Book statistics tables in the esd.whs.mil PDF archive are the primary source for the category counts and percentages; quote the exact breakdown from those tables rather than relying on secondary narratives that cherry-pick “unknowns” to imply intent. That one discipline changes the conversation from vibes to auditability.
Identified cases are easy to brief because they collapse uncertainty: a balloon, aircraft, astronomical object, or misperception fits into standard explanatory language. They also carry low reputational risk; officials can speak confidently and end the story.
Unknowns are hard to brief for reasons that have nothing to do with aliens. An “unknown” can mean missing sensor context, poor witness calibration, conflicting accounts, or classification constraints around how a detection was made. Public-facing personnel are left with a choice between over-explaining with fragile facts or under-explaining with minimal disclosure. Under-disclosure wins because it is safer, faster, and easier to keep consistent across offices.
The result is information asymmetry: the public gets a clean pile of identified explanations and a thin residue of unresolved items with little metadata. That asymmetry creates the impression that the residue must be the real story, even when the true driver is that uncertainty does not survive the public-release pipeline.
- Separate “no public data” from “no data exists.” A short statement and a closed case can still sit on a thicker internal file that never gets released.
- Track the bottleneck. Ask which office owned intake, which office owned adjudication, and which office cleared public language; centralized control predicts lag.
- Interrogate the incentive to close. Look for phrasing that signals administrative closure (“insufficient information”) rather than evidentiary resolution, and treat that as a different outcome than “identified.”
- Demand the missing metadata. Who collected what, with which sensors, at what times, under what chain of custody, and what was released versus withheld. That is how you evaluate process, not just conclusions.
Those patterns explain rapid dismissal, limited data release, and long lags as recurring outputs of systems and incentives. They do not explain every case, and they do not prove a single hidden cause. They do explain why a rule-bound process can reliably manufacture cover-up optics all by itself.
From Blue Book to AARO
The 1953 instinct that AFR 200-2 formalized-centralized authority over ambiguous aerial data-never really went away. It changed names and organizational charts, but it kept the same basic purpose: one controlled channel for intake, adjudication, and public-facing output.
Project Blue Book’s end state captures the template: a single, recognized intake point that could speak for the institution. Blue Book was terminated on December 17, 1969, and it was headquartered at Wright-Patterson Air Force Base, Ohio. Even when the reporting pipelines and investigative methods shifted over the years, the governing instinct stayed stable: pull reports into a controlled channel, have an official office validate what it can, and constrain what leaves the building as public-facing output.
The friction is structural, not rhetorical. Centralized handling protects operational equities, avoids contradictory statements across commands, and reduces the risk that raw, unvetted reports become public claims. The cost is predictable: outsiders experience the system as message discipline first and transparency second, because the institution prioritizes what it can responsibly stand behind as “the” narrative. The recurring disclosure argument about “who gets to speak” starts here, because the office that owns intake usually owns public framing.
Today’s discontinuity is not that centralization disappeared, but that it operates inside a denser interagency and technical environment. AARO is designated the DoD focal point and the authoritative office for UAP-related activities and may represent the Department to the interagency. That is a different mandate than a single-service program operating largely inside one chain of command.
The complication is the sensor ecosystem. Modern cases can touch radar, electro-optical and infrared video, electronic support measures, space-based cues, range instrumentation, and networked command-and-control logs. That increases evidentiary potential, but it also multiplies classification friction because each sensor, platform, and collection method carries its own protection rules. Interagency coordination also raises the number of legitimate stakeholders: military operators, the intelligence community, test and evaluation, and aviation safety all have equities in the same event record.
The resolving point is visible formalization. A publicly referenced mission brief titled “AARO_Mission_Brief_2025.pdf” signals a modern office that is expected to document process, scope, and outputs in a way that is legible beyond internal memos, including to oversight audiences.
More organizational boxes on a chart do not loosen classification rules. They often tighten them, because broader coordination forces earlier legal review, stricter handling, and clearer boundaries around what can be released without exposing sources and methods. Investigative integrity creates another constraint: an office that is tasked to resolve cases cannot publish partial data that contaminates witness follow-ups or encourages premature conclusions.
Competing equities are the third constraint. The same data packet can implicate aircrew safety, adversary collection risk, proprietary contractor systems, and foreign partner sensitivities. Centralized authority exists partly to adjudicate those conflicts, which is why disclosure fights keep returning to “data access” rather than office names.
Judge modern transparency by what AARO publishes, not by the fact that it exists. Watch for:
- Document types: case resolution reports, methodological memos, data-handling and deconfliction procedures.
- Verifiable specificity: date and time, general location, sensor types involved, and a clear chain of custody for primary data.
- Constraint clarity: what is withheld (and why), including explicit references to classification and source-protection limits rather than generic refusals.
Congress, whistleblowers, and disclosure bills
Centralization is only one side of the disclosure equation; the other is who can force records out of the channels that keep them controlled. That is why modern disclosure battles are fights over record control, not just beliefs about aliens.
The executive branch classifies, compartments, and stores national security records; Congress is the institution that can force those records into a review lane through subpoenas, appropriations, and statutory reporting requirements. That leverage is real, but it is also indirect: a hearing can surface allegations, while the underlying documentation stays inside Special Access Programs, Inspector General files, or agency record systems until Congress compels a defined production and a lawful declassification decision.
The House Oversight hearing titled “Unidentified Anomalous Phenomena: Implications on National Security, Public Safety and Government Transparency” occurred on July 26, 2023. David Grusch testified publicly under oath, which matters politically because it raises the cost of casual fabrication and justifies follow-up oversight. It did not, by itself, authenticate the underlying claims, because hearings are not classification review boards and they do not automatically produce the underlying records that would prove or disprove an allegation.
Grusch’s public testimony also needs to be read with a clean line between firsthand and secondhand statements. In his public account, he described his own work and interactions inside government as firsthand context, while his most explosive assertions about alleged crash retrieval and “non-human” material were presented as information he said he was told or shown through official duties, not events he personally witnessed. That distinction is the difference between a witness to events and a witness to what a system circulated internally.
The Schumer-Rounds UAP Disclosure Act proposal tried to change the default posture from “withhold unless forced” to “disclose unless a narrow, documented exception applies.” As introduced, its text framed the default this way: “There shall be a presumption of immediate disclosure of unidentified anomalous phenomena records.” Later NDAA-related text softened the immediacy and anchored disclosure to existing withholding authorities, shifting the operative standard to: “There shall be a presumption of disclosure of such records, subject to the exemptions under section 552(b) of title 5, United States Code.” That edit is not cosmetic; it moves the fight from a disclosure-first mandate to an exemptions-first terrain where agencies already have mature playbooks.
Separately, the NDAA for Fiscal Year 2023 includes provisions aimed at UAP reporting and whistleblowing, which is the practical response to legacy secrecy structures: you do not fix a records-control problem with rhetoric, you fix it with required reporting, defined recipients, and consequences for obstruction.
The Whistleblower Protection Act (WPA) provides statutory protections for federal employees who make protected disclosures, primarily by prohibiting retaliation and creating remedial paths. That baseline is not the same thing as an Intelligence Community clearance to discuss classified details publicly; IC personnel generally rely on IC-specific “lawful channel” pathways (for example, to an Inspector General) to report classified concerns without committing an unauthorized disclosure.
For Defense Department personnel, the DoD Office of Inspector General (DoD OIG) is a central intake point for reprisal allegations and publishes guidance on whistleblower protections and reprisal investigations. Mechanically, that matters more than a headline: it is where claims can be timestamped, documented, and routed for fact-finding inside the security rules that constrain public disclosure.
- Demand a clear reporting path: “Filed with DoD OIG,” “provided to an IC Inspector General,” or “submitted under a specific NDAA reporting provision” carries more weight than “went public.”
- Track what record sets Congress is targeting: subpoenas, SAP access requests, and mandated inventories are the pressure points, not viral clips.
- Verify the protection and penalty structure: credible disclosure efforts pair whistleblower protections with enforcement against retaliation and against hiding responsive records.
What transparency would require now
AFR 200-2 mattered because it normalized a workflow: centralized handling of reports and a public message shaped by what the system chose to surface. That same logic shows up later in Blue Book era scale-filtering, where volume and triage rules dictated what became “real cases” in the public record, and it shows up again in the AARO era, where formal lanes, clearances, and releasability decisions still govern what you get to see. Congressional pressure can change incentives, but it does not rewrite the default behavior of a security bureaucracy: it releases what it can defend, and it withholds what it cannot safely sanitize.
Meaningful transparency is not a mood; it is a repeatable process with records, standards, and enforceable review. AARO, Combatant Commanders, and the Services already require standardized reporting requirements and templates for UAP incidents, incursions, and engagements. The public standard should be simple: if a claim cannot be mapped to a documented case file built on those templates, it is not transparency, it is narrative. Demand reporting artifacts that make independent analysis possible:
- Verify a complete incident record with time stamps, geolocation, altitude or range estimates, and the reporting unit.
- Trace the sensor chain (platform, sensor type, settings where releasable, and any fusion steps) plus cross-sensor correlation claims.
- Document custody and integrity: who collected the data, who handled it, how it was stored, and what was changed (or not changed).
- Publish retention and disposition rules so “we no longer have it” is auditable, not convenient.
You can push this through the system that exists. Executive Order 13526 establishes the current uniform system for classifying and declassifying national security information (superseding EO 12958), which means agencies are operating under a defined framework, not an ad hoc secrecy culture. Mandatory Declassification Review (MDR) is the lever inside that framework: it allows any individual or entity to ask an agency to review specific classified records for possible declassification. FOIA is broader access law for agency records, but MDR is purpose-built to force a classification decision on the record itself, which is exactly what UAP controversies hinge on.
Hold the next “UFO sightings 2025” or “UFO sightings 2026” headline to one test: no case number, no standardized incident metadata, no custody and retention trail, and no EO 13526 grounded declassification pathway like MDR means no verified disclosure. That is the practical way to break the loop described at the start: treat every claim as an output of an information system, and judge it by the records and gates that system is designed to produce.
Sources / References
- Air Force Regulation 200-2, “Unidentified Flying Objects Reporting” (scan, 26 Aug 1953)
- Air Force Regulation 200-2 transcription and page scans (Wikisource)
- Report of the Scientific Panel on Unidentified Flying Objects (Robertson Panel), 17 Jan 1953 (CIA FOIA)
- Project Blue Book statistics tables (esd.whs.mil PDF)
- Executive Order 13526, Classified National Security Information (NARA/ISOO)
- Mandatory Declassification Review (MDR) guidance and training (NARA/ISOO)
- DoD memorandum establishing the All-domain Anomaly Resolution Office (AARO), 20 Jul 2022
- AARO Mission Brief (AARO_Mission_Brief_2025.pdf) — public PDF hosted on AARO website
Frequently Asked Questions
-
What is Air Force Regulation 200-2?
Air Force Regulation (AFR) 200-2 is an Air Force rule titled “Unidentified Flying Objects Reporting” that set official procedures for handling UFO reports and related public information. It was issued on 26 August 1953, amended by Change 200-2a on 2 November 1953, and exists in a later dated version on 12 August 1954.
-
Why did the Air Force treat UFO reports as a national security issue in 1953?
In the Cold War radar era, an “unidentified” report was operationally similar to a potential intrusion until proven otherwise, with nuclear-scale consequences for mistakes. High reporting volume also risked overwhelming controllers, intelligence officers, and intercept assets and amplifying public panic.
-
What did AFR 200-2 require the Air Force to do with UFO reports?
AFR 200-2 turned ad hoc UFO handling into enforceable procedure across all Air Force activities, covering reporting, interception, identification, and air search responsibilities tied to UFO events. Its system-level effect was centralized handling and controlled public messaging rather than local, improvised responses.
-
When could the Air Force talk to the media under AFR 200-2?
AFR 200-2 explicitly permitted informing news media representatives when an object is positively identified as a familiar object. That condition functions as a release gate that favors public statements about solved cases rather than unresolved ones.
-
How many UFO cases did Project Blue Book compile, and what years did it cover?
Project Blue Book’s archive reports 12,618 sightings or events compiled between 1952 and 1969. The program was terminated on December 17, 1969 and was headquartered at Wright-Patterson Air Force Base, Ohio.
-
What is AARO and when was it created?
AARO (the All-domain Anomaly Resolution Office) is a Department of Defense office designated as the DoD focal point for UAP-related activities. It was established by a DoD memorandum dated July 20, 2022, and is associated with artifacts like a mission brief file titled “AARO_Mission_Brief_2025.pdf.”
-
How do you evaluate whether a new UAP disclosure claim is credible?
Look for standardized incident artifacts: a complete case record with timestamps, geolocation, altitude/range estimates, the reporting unit, sensor types, and a documented chain of custody and retention/disposition rules. For declassification, the article points to Executive Order 13526 and Mandatory Declassification Review (MDR) as the practical pathway to force a record-level classification decision.